Users & User Groups Permissions
Anyone with an email can be added to your organization. We encourage everyone in your team to join FeatureHub as we believe both business and technical people will benefit from using it.
FeatureHub provides granular user permissions which can be assigned per application and even per environment through user groups and permissions.
Users
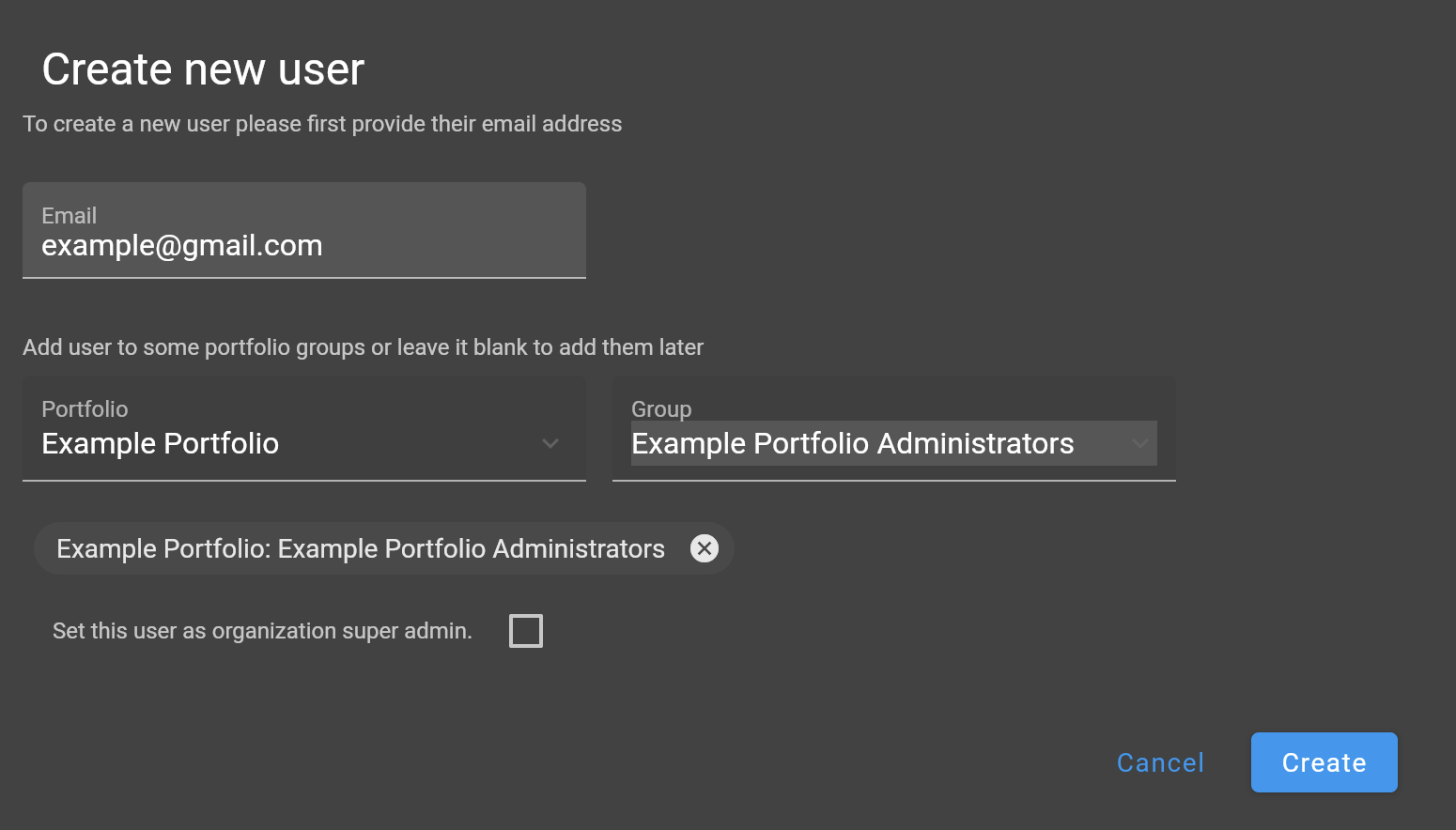
Users can be added to an organization by members with "Super Admin" permission. Once user is added, they can be assigned a group or multiple groups. User can also be assigned a "Super Admin" role. Editing of users details and deactivating users can be performed only by "Super Admins", however assigning those users to portfolio groups or removing them from the groups can also be done by users with "Portfolio Admin" role.
A user with "Super Admin" role cannot delete themselves from an organization. This is done for security reasons.
Registering for FeatureHub (only for non-SSO, SAML or social logins)
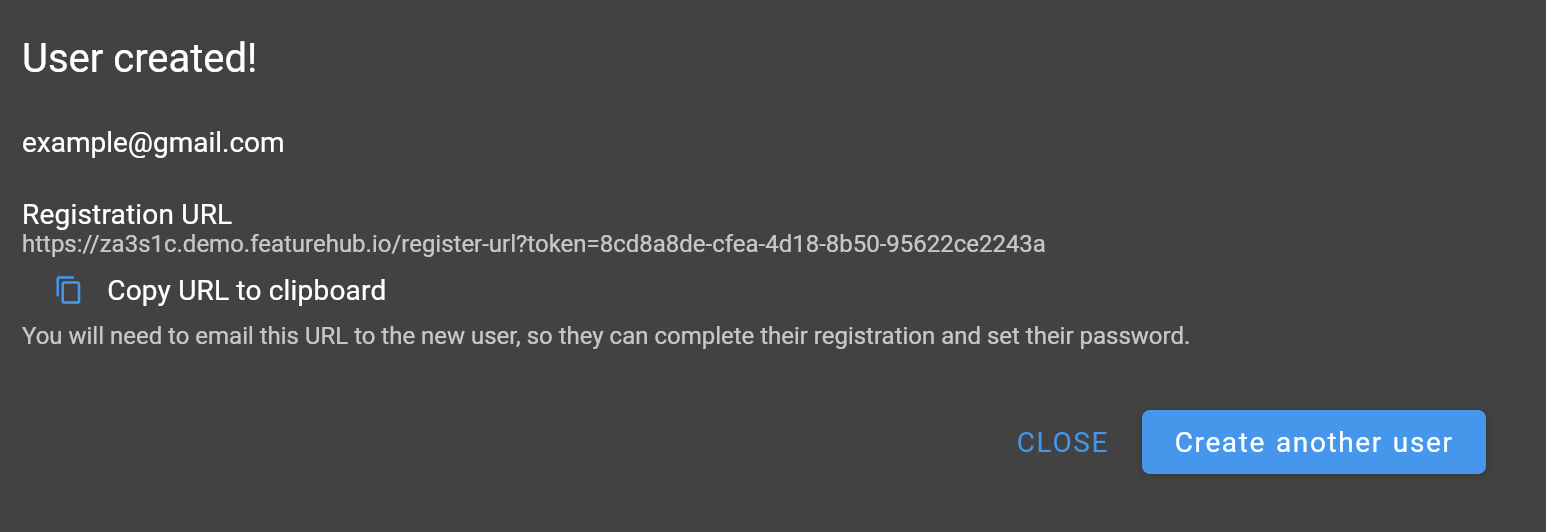
If you are using default identity option with the self-hosted FeatureHub instance, after you add a new user to the organization, you should copy the registration link and share it with the added user. They will be able to set their password and complete the registration.
Deactivating a user
If you would like to cancel user access to your FeatureHub app, select a "Delete" option. This will put their account status into "deactivated" state. Note, a user will be removed from all the groups once deactivated. If you decide to provide access to the same user again (with previously used email address), you can choose an option to "activate" a user from the users list. They will be able to log in with their previous credentials, or you can use reset password option to set a temporary password.
Password reset (only for non-SSO, SAML or social logins)
If a user forgets their password, it can be reset by "Super Admin" user to a temporary password. Share the temporary password with the user. They will be able to reset it to a permanent password next time they attempt to login.
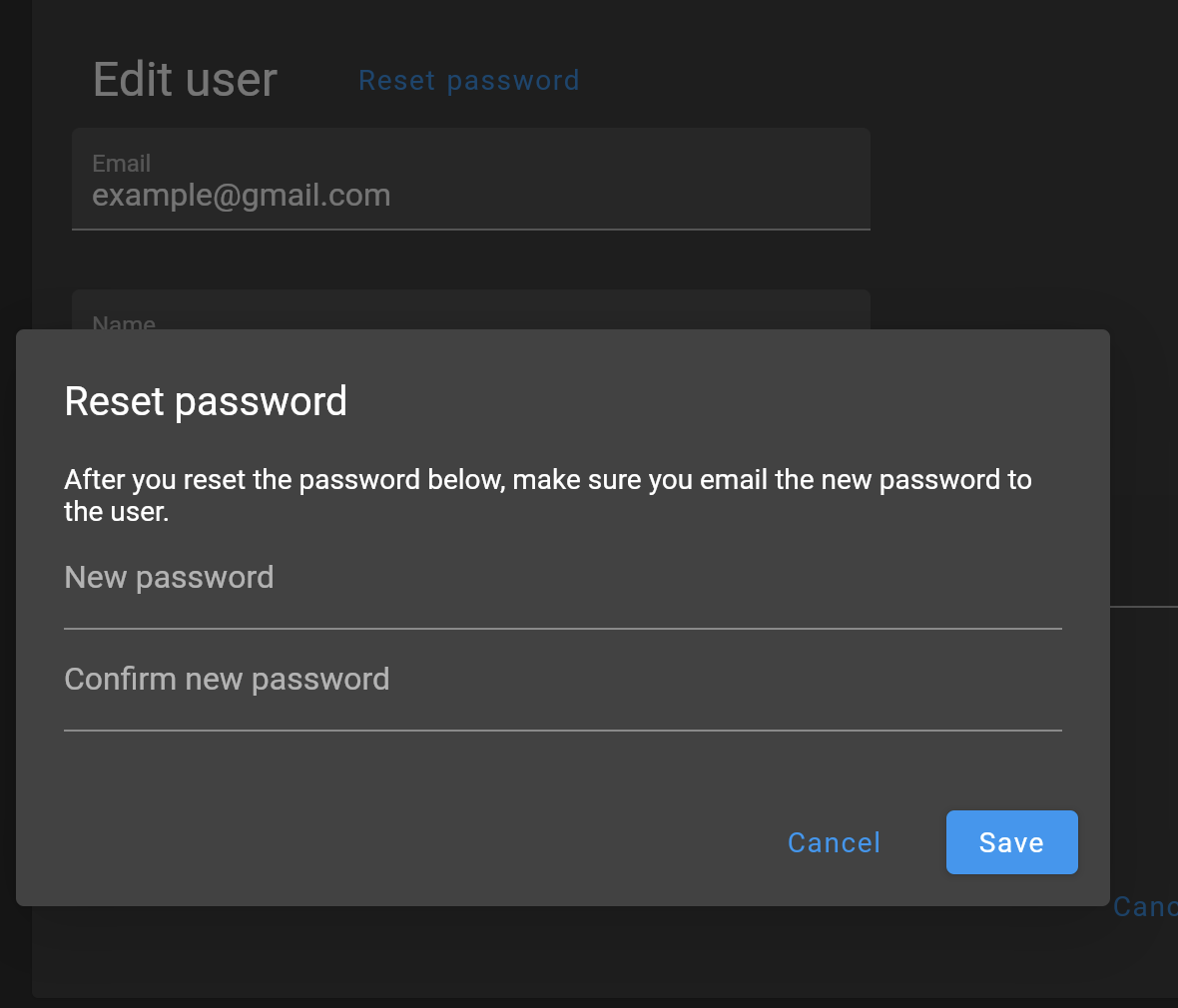
| FeatureHub doesn’t send emails to recover passwords or any registration or login related emails. We recommend having at least 2 users with super admin permissions, in case one of them forget their password. |
When there is only one Super Admin
When there is only a single Super Admin, and they have forgotten their password, the only way to reset it is to go to the database. To do this, in the database, find the id of the superuser in the fh_person table, and reset the password field to 1000:caffda0b26e265a0977718a548d784e6:1123a076c3925d0d77f2c902115e8732de25ae22394f74faaa52c8d9d9a829b8021299afd4a1793e47936445bb0ceff0f17f329716342db19f4e428dd5859dc1.
You can then login using the password featurehub.
User groups
Groups primary purpose is to control FeatureHub user access to the features in different portfolios, application and environments. Groups are created under a portfolio. You can create one or more groups and use them to set various permissions within the portfolio. Either use the same groups across applications within the portfolio, or create separate groups for each application. Some example groups might be:
-
Developers (Typically can create features and change feature values in non-production environments)
-
Testers (Typically can change feature values in non-production environments)
-
Operations (Typically can’t create or delete features but can update values in production)
| Every Portfolio automatically gets a group called "Administrators", Simply adding people to this group will make them administrators for this portfolio, and they automatically get all feature permissions in any application within that Portfolio. |
Once you create a group, you can add users in your organization to it.
You can also add Admin Service Accounts to the user groups for programmatic control via Admin SDK API
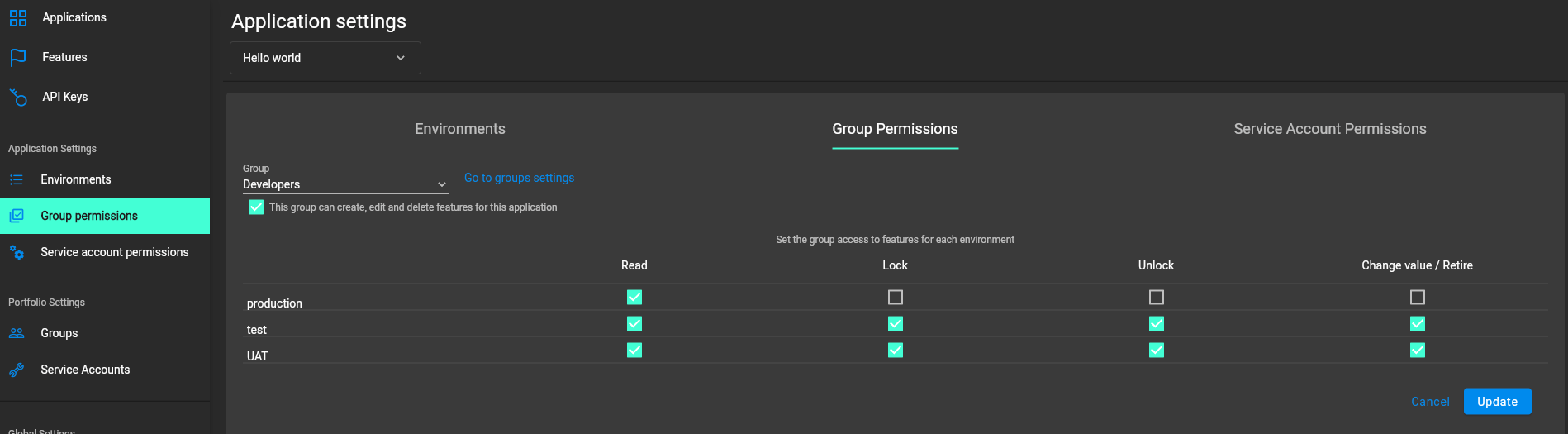
Group permissions to control features
For each application environment, there are permissions you can assign to portfolio groups
Feature level permissions
-
CREATE/EDIT/DELETE featuresThis permission allows all operations on a feature for a given application, including creating, updating and deleting entire feature. (Updating a feature includes feature properties updates:name,key,description,reference_link,metadata.)
| Once feature is created, feature values will be automatically created with default values in every environment for a given application. |
-
CREATE featureOnly allows to create features, editing and deleting of features is not permitted. -
NO FEATURE PERMISSIONSCreating, editing and deleting of features is not permitted.
Feature value level permissions
Following permissions are to control feature values and can be set per each environment for a given application:
-
READ-
Can view the value of a feature, feature value strategies assigned, feature properties, lock/unlock status, retirement status and feature auditing
-
Can view Feature Groups and settings for features and a strategy inside a group
-
-
LOCKCan lock a feature, so it’s value can’t be changed, this gives us a safety net when deploying incomplete code into production. (Typically, developers and testers keep features locked until they are finished and ready to be set by business people) -
UNLOCKCan unlock a feature, so it’s value can be changed -
CHANGE_VALUE-
Can change the value of a feature or can "retire" a feature.
-
Can create, set and delete strategy on a feature.
-
Can create, edit and delete feature groups for a given environment. Can change a feature value, create and update strategy in a Feature Group.
-
Administrator groups
There are two types of administrator groups that are available by default, Portfolio Admin and Organization Super Admin.
Portfolio Administrators
Portfolio Administrators permissions:
-
Create and manage portfolio groups
-
Create and manage applications
-
Create and manage environments
-
Create and manage features in any application and environment
-
Create and manage feature groups
-
Create and manage service accounts
-
Manage groups access to applications
-
Add and delete user from a group
| Every Portfolio automatically gets a group called "Administrators" on creation, simply adding people to this group will make them administrators for this portfolio. |
Organization Super Admin
Organization Super Admin permissions:
Inherits all permissions of "Portfolio Admin", plus all the following permissions:
-
Create and manage users of the system
-
Create and manage user groups
-
Create and manage portfolios
-
Create and manage Admin service accounts
| In other words, organization super admin has got all privileges, hence it is recommended to have at least 2 super admins, in case one of them leaves the organization. |